GlobalRiskInfo.com now on Twitter! February 11, 2012
Posted by Chris Mark in Risk & Risk Management.Tags: Chris Mark, globalriskinfo.com, InfoSec, Maritime Security, mark consulting group, markconsultinggroup.com
add a comment
“Slicing the Pie”; Risk Management 101 February 11, 2012
Posted by Chris Mark in Risk & Risk Management.Tags: black swan events, Chris Mark, combating piracy week, cybersecurity, data security, mark consulting group, markconsultinggroup.com, Risk & Risk Management, risk management, security
add a comment
 This is a followup to “Risk 101: an Introduction to Risk” Security, and Risk are interesting topics that lend themselves to endless debate (and the occasional argument). They are concepts that are bandied about quite frequently but, in my experience, are often not well understood by those using the terms. I have been asked by clients to describe risk management and security in business terms. At the risk of over simplifying the concepts, I will explain the concepts in this post. Security can be described rather simply as the implementation of controls to counter address a vulnerability or address a threat. Consider your house as an example. If you install a lock on the front door, you are implementing a control (the lock) to address a vulnerability (an unlocked door) and a threat (that an unauthorized person will enter).
This is a followup to “Risk 101: an Introduction to Risk” Security, and Risk are interesting topics that lend themselves to endless debate (and the occasional argument). They are concepts that are bandied about quite frequently but, in my experience, are often not well understood by those using the terms. I have been asked by clients to describe risk management and security in business terms. At the risk of over simplifying the concepts, I will explain the concepts in this post. Security can be described rather simply as the implementation of controls to counter address a vulnerability or address a threat. Consider your house as an example. If you install a lock on the front door, you are implementing a control (the lock) to address a vulnerability (an unlocked door) and a threat (that an unauthorized person will enter).
Risk can be described as the function of the likelihood of an event occurring and the impact should it occur. Risk can be quantified using a simple formula (R=P% x I$) or expressed qualitatively. In the scenario used above, there is a risk that your house will be burglarized. Depending upon where you live, and other factors, the likelihood (expressed in terms of probability) will vary from unlikely to more likely to very likely. The impact of the burglary will be determined by, among other things, the value of the assets that can be stolen. So how does this relate to security? The concepts are (or should be) inextricably entwined.
Controls should be implemented commensurate with the identified risk.
This is a very important concept. Consider the following scenario. If I were to offer you $1,000 to either 1) install a burglar alarm in your house or 2) install a fence to keep lions out of your yard, which option would you choose? Likely most readers would respond with the statement; “it depends upon where I live”. This demonstrates the example of security and risk management. There are two risks we are considering in this scenario. First, is the risk of burglary and second is the risk of lion attacks. If you live in the Kenyan bush, you may be more concerned about Lions as the probability is likely higher of a lion entering the yard then of a burglar. If you live in New York City you are likely more concerned about burglaries than lions as lions are not found in NYC (at least not legally). The controls you are considering are either a lock (to address the issues described previously) or a fence to address the threat of a lion entering the yard. Additionally, when we talk about ‘commensurate with the risk’ it means that the controls should be enough to address the risk but not too great. You would not put a $1,000 alarm system on a $500 car. It simply does not make sense and is an inefficient use of your limited resources.
With those topics covered very briefly, how do we discuss risk management from business terms? Easy. Consider that the risks to which you or your business are exposed are infinite. You may not believe there is a risk of being hit by a meteorite but I can assure you that as infinitesimally small as the chance may be, there is a chance (probability) and the impact is likely not very good (injury or death). If you question the example, read about the Sylacaugqa Meteorite here.
Now consider that the resources at your disposal (man hours, money, expertise, technology, information) is finite. You may have a huge budget, and world class expertise but the fact remains that you have finite resources to address infinite risks. The goal of risk management is to slice the pie of resources in a manner that allows you to address the greatest risks in the most efficient and effective manner possible. There are four primary methods of risk mitigation; Avoidance, Reduction, Sharing, and Retention or Acceptance. Using the burglary example.
Avoidance– You can ensure you don’t own anything that could be stolen. Or you could live in an isolated area where nobody else lives.
Reduction– You can reduce the risk (by reducing probability or impact) by installing locks or using a safe to protect your assets.
Sharing– You can get insurance for your assets to reimburse you if they are stolen.
Acceptance– you can simply accept the fact that burglary is a possibility but one you are willing to accept if the likelihood is remote or you have no assets to steal.
The idea is to allocate the pieces of pie (which represents your finite resources) in a manner to address as much of the risk as possible. It should be noted that there will always be residual risk and the possibility of Black Swan events.
Armed Security; Increasing Competition & Decreasing Demand February 10, 2012
Posted by Chris Mark in Industry News, Piracy & Maritime Security, Risk & Risk Management.Tags: Anti Piracy, armed security, Chris Mark, economics, ICoC, Maritime Security, mark consulting group, somali pirates
1 comment so far
 Recently I wrote about the armed security market and the inevitable shakeout. A look at the most recently data supports this position and does not seem to fare well for the new entrants into the maritime security space. As of February 1st, 2012 there are now 307 signatories of the ICOC with 55 signing on December 1st, 2011 and another 42 signing on February 1st, 2012. While some of those signing are older, more established companies there is a large percentage of new entrants. In short, competition is becoming fierce within the maritime security industry.
Recently I wrote about the armed security market and the inevitable shakeout. A look at the most recently data supports this position and does not seem to fare well for the new entrants into the maritime security space. As of February 1st, 2012 there are now 307 signatories of the ICOC with 55 signing on December 1st, 2011 and another 42 signing on February 1st, 2012. While some of those signing are older, more established companies there is a large percentage of new entrants. In short, competition is becoming fierce within the maritime security industry.
In January, 2012 the IMB released statistics on pirate attacks and hijackings. From 2010-2011 pirate attacks in and around Somalia increased roughly 7.5% from 219 to 237 while at the same time hijackings decreased roughly 43% from 49 to 28. In 2010 approximately 22% of the ships attacked were taken and hijacked while in 2011 the percentage dropped to just below 12%. A combination of increased naval patrols, armed guards, and implementation of BMP is having a desired effect on hijackings.
There are several things that can be surmised from the information above. First, competition within the maritime security industry is increasing rapidly. With the wars winding down in Iraq and Afghanistan there is an increasing number of veterans entering the job market. Some of these are founding security and maritime security companies to try take advantage of the perceived demand for the services. This will have the effect of decreasing rates across the industry unless demand increases, as well. The second thing that can be surmised is that demand for maritime security is likely to decrease significantly. There are several reasons to anticipate a decrease. As current efforts are showing success companies will logically begin to evaluate the need for expensive, armed guards when other controls may prove sufficient. Additionally, it is expected that the number of ‘free riders’ will increase as companies begin to hedge their bets and forgo the use of security with the belief that other companies investment will have a residual affect on their security. Finally, insurance rates should drop for ships traversing high-risk waters making the justification for the cost of engaging armed security more difficult. As any first year economics student can attest; increasing competition and decreasing demand does not bode well for the industry. Companies will have to drop their prices to compete for a rapidly decreasing pool of potential clients. The end result is the inevitable shakeout of the industry.
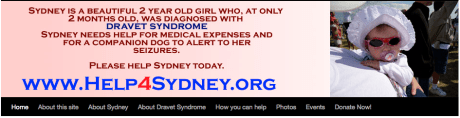
Help4Sydney.org – Help a Former Marines’ Daughter February 8, 2012
Posted by Chris Mark in Uncategorized.Tags: dravet, epilepsy, help4sydney.or sydneyagainstdravet.com, sydney, sydney michaels
add a comment
Sometimes we need to deviate from the usual discussion on risk and security. Today is one of those days. As many of this blogs’ readers are former military, I thought it prudent to pass this on.
An old friend of mine from the Marines has a daughter that is very sick. She has what is known as Dravet’s Syndrom which is a very, very severe form of epilepsy that is, unfortunately, incurable. As the father of a 2 year old myself, I am heartbroken for the family. Please visit the site and watch the video about Sydney and learn a bit about Dravet’s Syndrome.
If you feel compelled, please donate to help the family with their medical bills or pass the link on through facebook or some other means. The more traffic we get the better. Thank you in advance for your help!
Why Regulation Cannot Prevent CyberCrime (TransactionWorld) February 6, 2012
Posted by Chris Mark in InfoSec & Privacy, Laws and Leglslation, Risk & Risk Management.Tags: Chris Mark, cybercrime, cybersecurity, InfoSec, Maritime Security, risk management, security, transaction world
add a comment
 As the maritime industry is increasingly focused on protection of data assets, I thought it would be beneficial to include an article on the topic. This article is one I wrote for TransactionWorld in July, 2011. It is titled: “Why Regulation Cannot Prevent CyberCrime” and is a continuation on the discussion of the impact of deterrence on behavior.
As the maritime industry is increasingly focused on protection of data assets, I thought it would be beneficial to include an article on the topic. This article is one I wrote for TransactionWorld in July, 2011. It is titled: “Why Regulation Cannot Prevent CyberCrime” and is a continuation on the discussion of the impact of deterrence on behavior.
“Data security and privacy regulation have increased significantly over the past 10 years. The U.S. now has 46 state breach notification laws and there have been numerous bills introduced in Congress that propose to regulate personally identifiable information and to dictate security of such data. In spite of this increasing regulation, data breaches continue to plague the industry. Some have proposed that more regulation is the answer. Unfortunately, regulation alone is inadequate to prevent data theft and protect data.
At its core, data theft and network intrusions are crimes. At the risk of oversimplifying the work of criminologists, crime prevention can be summarized as using deterrents to affect protection of assets and prevention of theft. Protection applies to the ‘hardening’ of targets by implementing controls that increase the level of difficulty of perpetrating a crime. A vault is a good example of a protective measure. While no vault is completely impenetrable, vaults do provide significant protective value. Data security controls are protective measures. They are designed solely to limit attempts to obtain the target of value. Without a deterrence effect, criminals are free to attack companies at will without fear of retribution. This article will explore the value of deterrence in the prevention of crime.” (read full article here)