“Why does the FBI have your UDID (and 12.4 million more)?” FBI Laptop Hacked…1 million Apple IDS posted online September 4, 2012
Posted by Chris Mark in cyberespionage, cybersecurity.Tags: anonymous, Apple, Christopher Stangl, Cyber Action Team, data breach, fbi, Hacked, mark consulting group, UDID
add a comment
*UPDATE* It was reported yesterday that the FBI laptop was not, in fact, the source of UUIDs that were hacked. A company called Blue Toad revealed that it was the source of the stolen ids. It’s not clear how the data was stolen from Blue Toad or what, if any relationship exists between the company and the laptop that was first identified as the source of the breach.***
According to NBC News, hackers associated with the anti-government group AntiSec have hacked an FBI Agent’s laptop and posted over 1 million Apple Unique Device Identification Number or UDIDs online. The Apple UDID is used by Apple to determine what applications are running and to lock down the phones, IPads and computers from other applications. Alone, they do not represent personally identifiable information but However, New Zealand-based security researcher Aldo Cortesi has shown that thanks to disregard of Apple’s security guidelines by iOS game and app developers, it’s possible to determine a user’s identity through an UDID alone. According to the story:
“The Pastebin post claims that the UDIDs were stolen thanks to an Anonymous hack into the laptop of FBI agent Christopher Stangl, a member of a New York-based cybercrime task force. “During the second week of March 2012, a Dell Vostro notebook, used by Supervisor Special Agent Christopher K. Stangl from FBI Regional Cyber Action Team and New York FBI Office Evidence Response Team was breached using the AtomicReferenceArray vulnerability on Java,” the posting states. “During the shell session some files were downloaded from his Desktop folder one of them with the name of ‘NCFTA_iOS_devices_intel.csv’ turned to be a list of 12,367,232 Apple iOS devices including Unique Device Identifiers (UDID), user names, name of device, type of device, Apple Push Notification Service tokens, zipcodes, cellphone numbers, addresses, etc. the personal details fields referring to people appears many times empty leaving the whole list incompleted on many parts.”
Why the FBI has such a list of over 12 million UDIDs is an interesting question. Why the list would be on a laptop is another interesting question. To check whether your iPhone, iPad or iPod Touch’s UDID might be among those affected, a Unix developer based in Florida has already posted a tool: http://kimosabe.net/test.html
“Here I (we) go Again…”; GlobalCerts.net hacked August 27, 2012
Posted by Chris Mark in cybersecurity.Tags: anonymous, cyber war news, data breach, globalcert.net, hack, mark consulting group, PCI DSS, security
add a comment
 On this lovely Monday morning on the opening week of College Football (WAR EAGLE!)…I open with some classic Whitesnake and their awesome song from 1987: “Here I go Again”. It seemed appropriate since here ‘we’ go again with another hack and data compromise. According to Cyber War News, GlobalCert.net was hacked and their data posted to Pastebin..according to the report, GlobalCert.net’s web database was hacked and over 1000 clients’ data posted online by Anonymous. GlobalCert.net’s website says the following about their website:
On this lovely Monday morning on the opening week of College Football (WAR EAGLE!)…I open with some classic Whitesnake and their awesome song from 1987: “Here I go Again”. It seemed appropriate since here ‘we’ go again with another hack and data compromise. According to Cyber War News, GlobalCert.net was hacked and their data posted to Pastebin..according to the report, GlobalCert.net’s web database was hacked and over 1000 clients’ data posted online by Anonymous. GlobalCert.net’s website says the following about their website:
“GlobalCerts provides a comprehensive solution that meets a full range of secure messaging needs—including an automatic, transparent, inter-organizational secure messaging product, the SecureMail Gateway. GlobalCerts also offers a trusted, scalable, user friendly solution to overcome the hurdle obstructing many organizations from deploying a standards-based, secure messaging solution. SecureTier is a hands-off global, certificate management solution for key creation, discovery, and revocation. No other key distribution and discovery system is as effortless and efficient as GlobalCerts’ solution.”
Seems that GlobalCert.net should practice what they preach 😉
Oil Giants Hacked by Anonymous in “Save the Arctic Phase2” July 16, 2012
Posted by Chris Mark in Data Breach, Industry News.Tags: anonymous, bp, cybercrime, cybersecurity, data breach, exxon, InfoSec & Privacy, mark consulting group, savethearctic, security
add a comment
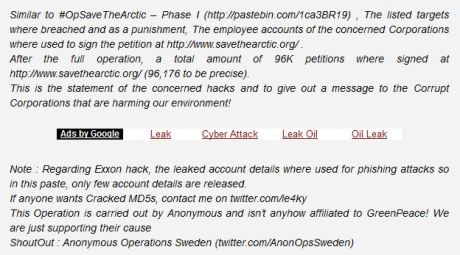
 According to CyberWarNews.com Anonymous set its sites on oil giants Shell, BP, Gazprom, and Rosneft in what has been dubbed “Save the Arctic Phase 2”. This comes on the heels of phase one in which account details including administrator accounts, passwords and other server info was stolen from Exxon and released.
According to CyberWarNews.com Anonymous set its sites on oil giants Shell, BP, Gazprom, and Rosneft in what has been dubbed “Save the Arctic Phase 2”. This comes on the heels of phase one in which account details including administrator accounts, passwords and other server info was stolen from Exxon and released.
According to the messages posted on pastebin, the account were used to sign the petition on savethearctic.org and, more disturbingly, for phishing attacks. Hacktivism is a growing concern for all companies. Whether it be to combat the perceived unfair distribution of wealth of capitalism, support of US defense industry, or environmental issues, hacktivists are increasingly active against corporations.
“The Rise of CyberEspionage” – Chris Mark Published in Homeland Security Network June 18, 2012
Posted by Chris Mark in cyberespionage, cybersecurity.Tags: anonymous, china, cybercrime, cyberespionage, cybersecurity, data breach, data security, homeland security network, L3, mark consulting group, RSA, security
add a comment
 An article I wrote on the Rise of Cyber Espionage was picked up by the Homeland Security Network. I must admit that the article title is not what was submitted but the article is one I wrote. If you are interested, spin on over to the Homeland Security Network and read the article. Any feedback would be appreciated..here is an excerpt:
An article I wrote on the Rise of Cyber Espionage was picked up by the Homeland Security Network. I must admit that the article title is not what was submitted but the article is one I wrote. If you are interested, spin on over to the Homeland Security Network and read the article. Any feedback would be appreciated..here is an excerpt:
“On April 15, 2011, the US Congressional Subcommittee on Oversight and Investigations conducted a hearing on Chinese cyber-espionage. The hearing revealed the US government’s awareness of Chinese cyberattacks. In describing the situation in her opening remarks, sub-committee chairperson Dana Rohrbacher astutely stated:
“[The]United States is under attack.”12 “The Communist Chinese Government has defined us as the enemy. It is buying, building and stealing whatever it takes to contain and destroy us. Again, the Chinese Government has defined us as the enemy.”
(UPDATE)-“Interesting” Logic & Analysis – Verizon’s 2012 Data Breach Report April 17, 2012
Posted by Chris Mark in Industry News, InfoSec & Privacy, terrorism.Tags: anonymous, Chris Mark, CSOonline, cybercrime, hacktivism, InfoSec, mark consulting group, security, Verizon data breach report
2 comments
I received a very insightful comment from one of the Verizon authors and thought it prudent to share. I think this explanation is very helpful for companies looking at infosec controls. Here it is, in part(emphasis added): “You make a valid point about the fact that a determined attacker would simply try again if the first attempt failed. However, our finding that most breaches are avoidable through relatively simple controls doesn’t overlook this as you suggest. Our data show that most criminals aren’t determined to breach a particular victim and likely won’t try again if met with decent resistance. In fact, the extreme opportunistic nature of target selection means they likely won’t even be attacked w certain controls in place because automated probes will skip on down the street after jiggling the door handle a bit.“ You can read the full comment, in ‘comments’. The entire post is you continue reading. (more…)