“Money Laundering May Support Drugs and Terror Funding?” – US Senate says of HSBC July 17, 2012
Posted by Chris Mark in Industry News, Risk & Risk Management, terrorism.Tags: AML, HSBC, mark consulting group, PATRIOT, risk, security, senate, terrorism
add a comment
 According to a US Senate Report issued today and major news outlets including MSNBC, Europe’s largest bank, HSBC, has “A “pervasively polluted” culture at HSBC allowed the bank to act as financier to clients moving shadowy funds from the world’s most dangerous and secretive corners, including Mexico, Iran, Saudi Arabia and Syria, according to a scathing U.S. Senate report issued on Monday.” The report, titled: US Vulnerabilities to Money Laundering, Drugs, and Terrorist Financing: HSBC Case History “…examines the anti-money laundering (AML) and terrorist financing vulnerabilities created when a global bank uses its U.S. affiliate to provide U.S. dollars, U.S dollar services, and access to the U.S. financial system to high risk affiliates, high risk correspondent banks, and high risk clients.” The US Enacted stronger Anti Money Laundering laws as a part of the PATRIOT act passed in the wake of 9/11. These AML laws were designed to cut of the flow of money to terrorists. In the case of HSBC it appears many of the rules were ignored potentially allowing drug cartels and terrorist to move and launder money.
According to a US Senate Report issued today and major news outlets including MSNBC, Europe’s largest bank, HSBC, has “A “pervasively polluted” culture at HSBC allowed the bank to act as financier to clients moving shadowy funds from the world’s most dangerous and secretive corners, including Mexico, Iran, Saudi Arabia and Syria, according to a scathing U.S. Senate report issued on Monday.” The report, titled: US Vulnerabilities to Money Laundering, Drugs, and Terrorist Financing: HSBC Case History “…examines the anti-money laundering (AML) and terrorist financing vulnerabilities created when a global bank uses its U.S. affiliate to provide U.S. dollars, U.S dollar services, and access to the U.S. financial system to high risk affiliates, high risk correspondent banks, and high risk clients.” The US Enacted stronger Anti Money Laundering laws as a part of the PATRIOT act passed in the wake of 9/11. These AML laws were designed to cut of the flow of money to terrorists. In the case of HSBC it appears many of the rules were ignored potentially allowing drug cartels and terrorist to move and launder money.
In a statement emailed to NBCNews.com, the bank said:
We will apologize, acknowledge these mistakes, answer for our actions and give our absolute commitment to fixing what went wrong. We believe that this case history will provide important lessons for the whole industry in seeking to prevent illicit actors entering the global financial system.
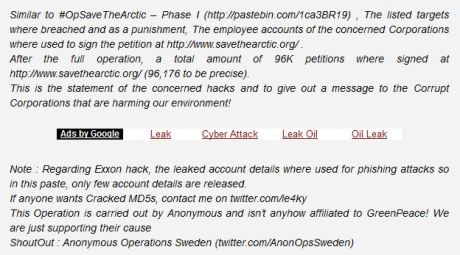
Oil Giants Hacked by Anonymous in “Save the Arctic Phase2” July 16, 2012
Posted by Chris Mark in Data Breach, Industry News.Tags: anonymous, bp, cybercrime, cybersecurity, data breach, exxon, InfoSec & Privacy, mark consulting group, savethearctic, security
add a comment
 According to CyberWarNews.com Anonymous set its sites on oil giants Shell, BP, Gazprom, and Rosneft in what has been dubbed “Save the Arctic Phase 2”. This comes on the heels of phase one in which account details including administrator accounts, passwords and other server info was stolen from Exxon and released.
According to CyberWarNews.com Anonymous set its sites on oil giants Shell, BP, Gazprom, and Rosneft in what has been dubbed “Save the Arctic Phase 2”. This comes on the heels of phase one in which account details including administrator accounts, passwords and other server info was stolen from Exxon and released.
According to the messages posted on pastebin, the account were used to sign the petition on savethearctic.org and, more disturbingly, for phishing attacks. Hacktivism is a growing concern for all companies. Whether it be to combat the perceived unfair distribution of wealth of capitalism, support of US defense industry, or environmental issues, hacktivists are increasingly active against corporations.
“Experts Around Every Corner; Part Deux” -Safes, Security, Expertise and Ignorance July 16, 2012
Posted by Chris Mark in Uncategorized.Tags: cybersecurity, expertise, information security, mark consulting group, risk management, safes, security, will rogers
add a comment
 “There is nothing so stupid as an educated man. If you get him off the thing he was educated in.” – Will Rogers
“There is nothing so stupid as an educated man. If you get him off the thing he was educated in.” – Will Rogers
This weekend I was reading a major news source and I was struck by an article on Safes. As I have a gun safe, and other safes, I thought it would be interesting to read. I have written posts before on expertise (Experts in every room). Various ‘expert’s are interviewed in the article. One in particular stood out. He said: “People need to wake up. They think they are protecting themselves, but they may actually be putting themselves at more risk,” As this was a very pointed statement (People need to wake up!)…I immediately thought that my own strategy of securing my valuables was mis directed. I continued reading to see who this expert was…He then said: “Sure you want to have some cash at home, but more than a little feels unsafe,” (I have added the bold)…the expert was a man named Michael Cresh…what is his job? You are probably thinking police officer, security expert, safe expert, or something similar. You would be mistaken. He is a Certified Financial Planner. If I were asking for financial planning, this is the person that I would turn to. If I am considering the purchase of a safe, I can safely say (pun intended) I could not care less what a CFP has to say unless he has some other level of expertise. His statement belie his ‘expertise’ and demonstrate he has little understanding of physical security or risk analysis as it pertains to physical security. (…feels unsafe).
When considering a security professional that proclaims expertise, take a very close look. Whether maritime security, information security, personal security, or any other area of security there are more than a few self proclaimed experts walking the halls.
Last year I wrote a paper for companies to use when evaluating expertise in the maritime security industry. While focused on maritime security it is relevant to all areas of expertise. You can read the article here.
“123456, password, welcome” – Yahoo Password Posted Online July 12, 2012
Posted by Chris Mark in News, PCI DSS, Risk & Risk Management.Tags: data breach, encryption, hash, InfoSec, markconsultinggroup.com, password, risk, security, yahoo
add a comment
 A story today on MSNBC says that Yahoo Voices was compromised and 450,000 usernames/password posted online. Not surprisingly, the passwords were not hashed or otherwise protected using encryption. While the posting of passwords is nothing new what is interesting is what the researchers found when looking at user generated passwords. The most common passwords were ‘123456’ followed by ‘password’ and ‘welcome’. Fully 1/3 of the passwords used lower case letters only. Here is where I get on my soapbox. According to the story:
A story today on MSNBC says that Yahoo Voices was compromised and 450,000 usernames/password posted online. Not surprisingly, the passwords were not hashed or otherwise protected using encryption. While the posting of passwords is nothing new what is interesting is what the researchers found when looking at user generated passwords. The most common passwords were ‘123456’ followed by ‘password’ and ‘welcome’. Fully 1/3 of the passwords used lower case letters only. Here is where I get on my soapbox. According to the story:
“Yahoo! Voices’ administrators made a big mistake storing the passwords in plaintext, but all users need to bolster their own security as well. Make passwords harder to guess by making them more than eight characters long, and pepper them with upper-case letters, numbers and punctuation marks.”
First, strong passwords would not have helped because YAHOO WAS STORING THEM IN CLEARTEXT!..and they were stolen! Second, the company should enforce strong passwords. While all users should use strong passwords, when dealing with 450K users it is prudent to understand that either some users aht a will not understand what a strong password is or will simply ignore the directions. Yahoo should have forced strong passwords…